This is another post in our series about advanced footprints and how to avoid them in PBN hosting. While we wouldn’t really count nameserver footprints as advanced, there are still people doing really basic mistakes with them so we wanted to shed some light on the topic.
Nameservers are servers hosting your DNS zone file, or in other words, your DNS records. Without them, your browser does not know to which server to send your request for domains you type in the address bar.
Everybody knows there is a reverse IP search. But did you know there is also a reverse nameserver search? It does the same thing as reverse IP – shows all websites on that nameserver.
Why nameservers are more important than IPs
Although a lot of people see IPs as a big footprint with PBNs, there are multiple reasons why nameservers are a more problematic footprint for deindexation than IPs.
- IPs are often shared, SEO host’s nameservers are not,
- IPs change hands very quickly, SEO host’s nameservers do not,
- IPs are owned by reputable hosting provider, SEO host’s nameservers are not.
One common thread in all the above points is that nameservers are usually owned by the SEO host, while IPs are something that all hosting providers have to share. Why? Because the Internet has run out of IPv4 IPs.
Because of the above reasons, years ago websites on SEO hosts got deindexed based on their nameservers, not IPs.
Five Approaches To Using Nameservers For PBNs
(1) Using nameservers provided by brand hosting providers themselves, such as Digital Ocean, Linode, Rackspace, Amazon, etc.
Example: ns1.digitalocean.com, ns2.linode.com, dns1.stabletransit.com, ns-812.awsdns-00.net. These nameservers are shared among thousands upon thousands of legitimate sites so they are completely SAFE to use for your PBN.
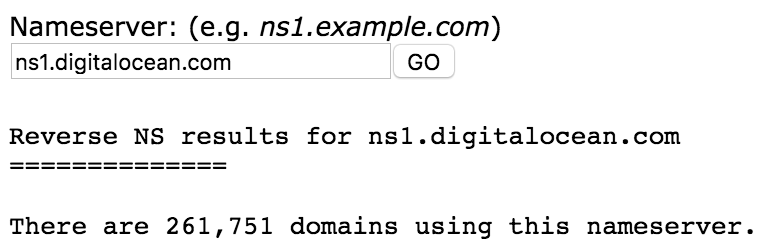
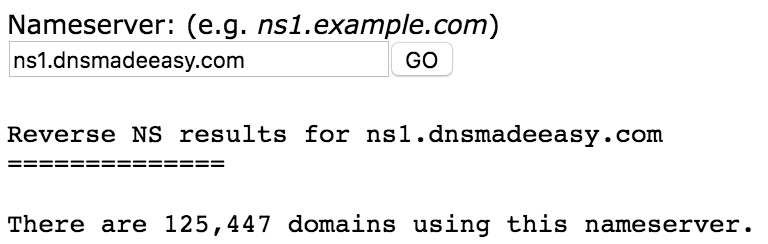
(2) Using nameservers provided by Third-Party DNS providers, such as ClouDNS, DNS Made Easy, DNSimple, World Wide DNS, etc.
Example: ns11.cloudns.net, ns2.dnsmadeeasy.com, ns4.dnsimple.com, ns3.worldwidedns.net. Like nameservers of brand hosting providers, these too are shared among thousands of websites and are completely SAFE to use for your PBN.
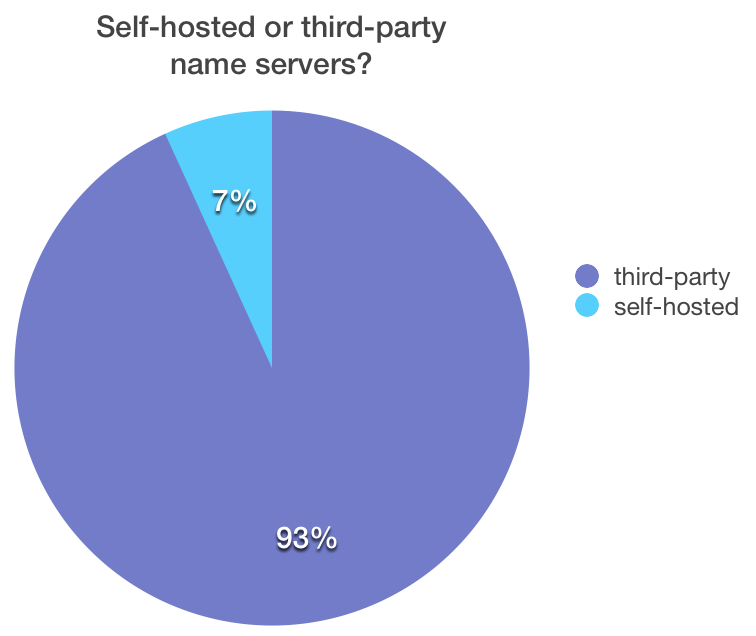
(3) Using self-hosted nameservers for each domain. For example, if you have the domain myblog.com, you would use ns1.myblog.com and ns2.myblog.com as nameservers. This in itself is not a problem if you do it from time to time, but it is DANGEROUS to use on the majority of your PBN sites. Why? Well, out of 1 million top sites by Alexa, only 7% are using this approach. You do not want your PBN’s percentage to be much higher.
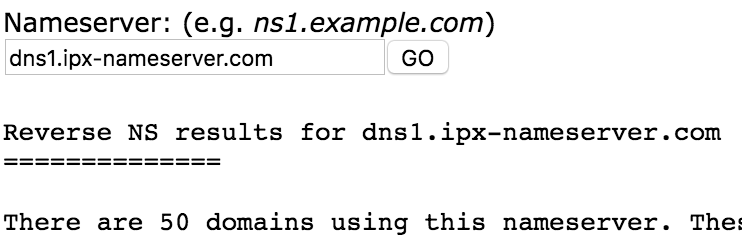
(4) Using your SEO host’s nameservers. SEO Hosts will normally purchase random domains and set up nameservers on these domains. There are several major problems with this approach:
- All nameservers’ domains’ whois records point to the same company, the SEO host.
- You PBN sites are in a really bad DNS neighbourhood. You can do a quick reverse nameserver search on an SEO Host’s nameserver and you will see what we mean. There are only and solely SEO sites using the nameserver.
Because of the reasons listed above, it is VERY DANGEROUS to use SEO Host’s nameservers for your PBN.
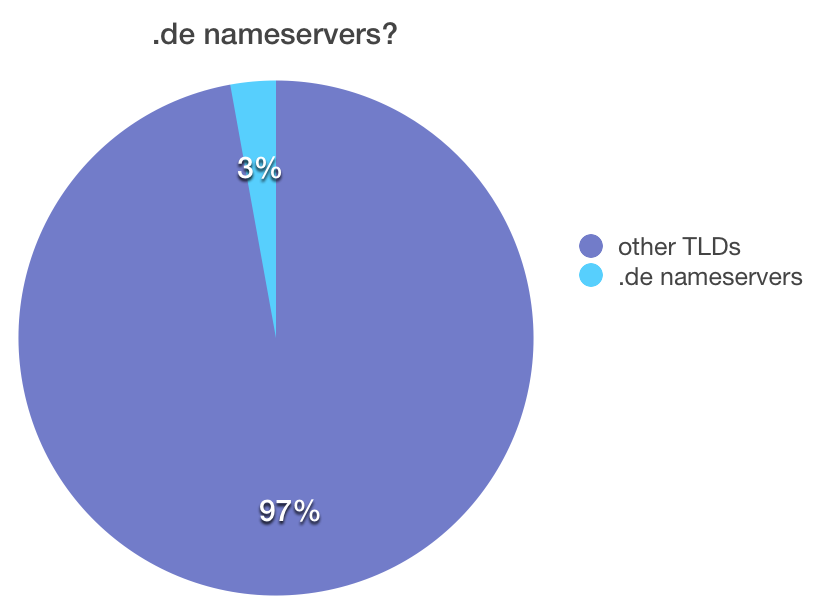
(5) Some SEO hosting providers will use German (.de) domains for their nameservers, because German domains hide Whois information. But again, only a very small fraction of websites out there use German nameservers. Among Alexa top 1 million domains, only 3% use German nameservers, so it is VERY DANGEROUS to use German nameservers on the majority of your PBN sites.
Summary
While this blog post may sound like a defense of EBN, it is actually something we thought about before building EBN. It is how legit websites are using DNS and that is why we built it like this.
More than one EBN competitor is using the dangerous approaches described above. Be vigilant, test the nameservers provided to you! They should be from the hosting or popular third-party providers and should have a clean DNS neighborhood (check the nameservers you are using). Google used nameservers to deindex SEO hostings a few years back – not IPs. And, if you haven’t yet, read myths about PBN footprints to clear some other misconceptions and how to improve blog security.
